Microsoft Exchange servers are common target for threat actors not only because they provide multiple entry points but because they offer opportunities for persistence and domain escalation as they are bind to the Active Directory. Compromising the domain of the organisation via Exchange connections can become a trivial task especially if a number of security controls are missing.
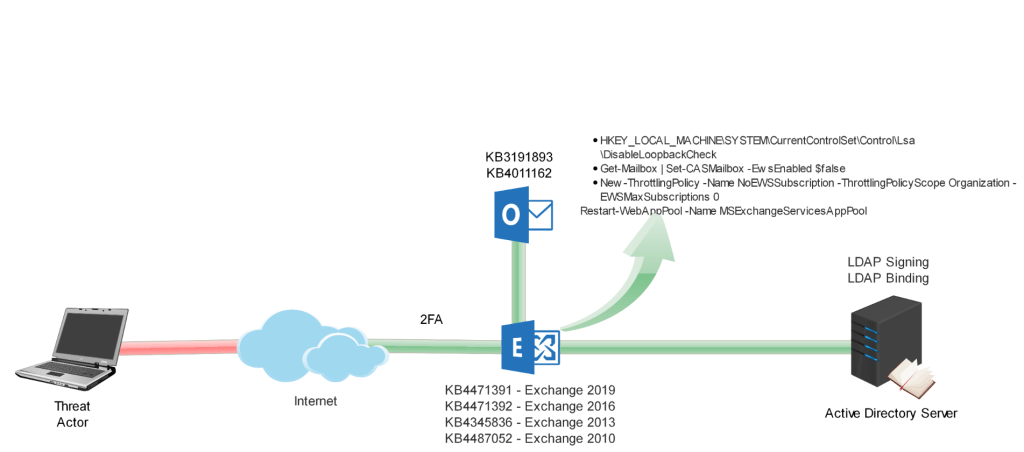
The following diagram demonstrates real world attacks that are implemented by threat actors in order to achieve full domain compromise by abusing Exchange services, Exchange API and standard Outlook functionality.
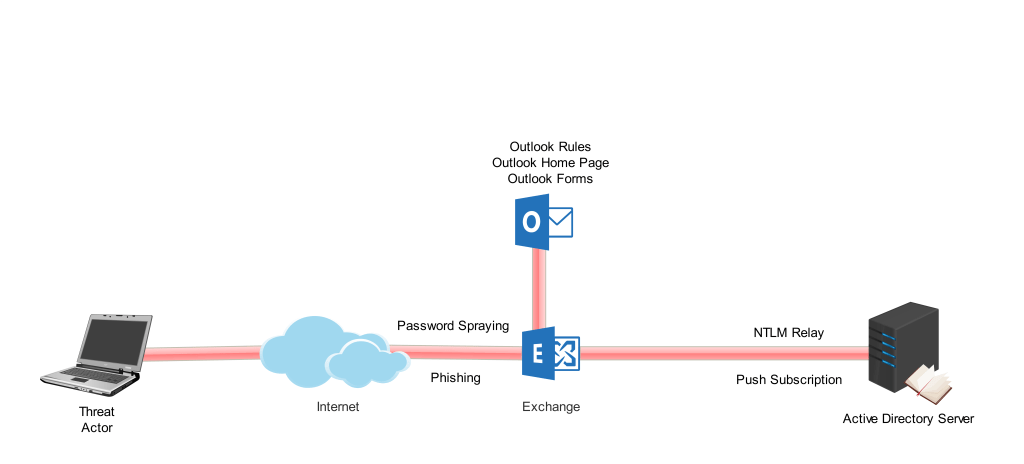
Blocking these attacks require a series of measures that organisations should implement to reduce the risk of a security breach via Microsoft Exchange connections. These measures include:
- Disabling Unecessary Services
- Enabling 2-Factor Authentication
- Enabling LDAP Signing & LDAP Binding
- Apply Critical Security Patches & Workarounds
Disable Unecessary Services
Default installations of Microsoft Exchange have the following services enabled:
- Outlook Web Access (OWA)
- Exchange Web Services (EWS)
- Exchange ActiveSync (EAS)
All of these services create an attack surface that threat actors could benefit by conducting attacks that could lead to discovery of legitimate credentials, getting access to mailbox of users and perform domain escalation. Outlook Web Access provides the ability to domain users to access their mailbox externally. However Exchange Web Services and Exchange ActiveSync should be evaluated if they are required by the business.
Exchange Web Services permit client applications to communicate with the Exchange server. Access should be disabled if EWS doesn’t serve a specific business requirement. Executing the following command from Exchange Management Shell will disable access for all mailboxes.
Get-Mailbox | Set-CASMailbox -EwsEnabled $false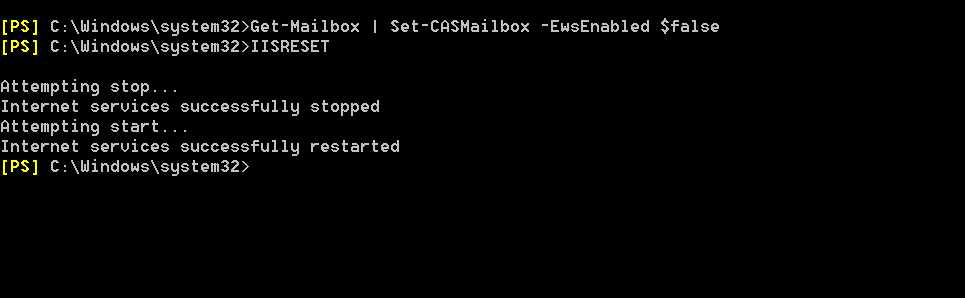
Disable EWS Access
ActiveSync protocol allows mobile devices of domain users to synchronise data (mail, calendar, contacts and tasks) with Exchange mailboxes. If this protocol is not required by the business it should be disabled.
Get-Mailbox | Set-CasMailbox -ActiveSyncEnabled $false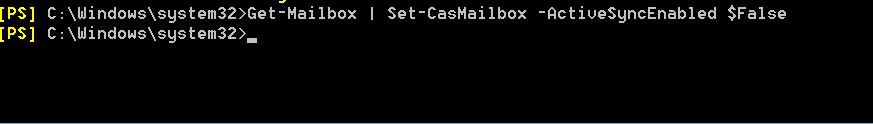
Disable ActiveSync
Authentication should be also disabled to reduce the attack surface of threat actors during password spraying attacks.

Disable EWS Authentication 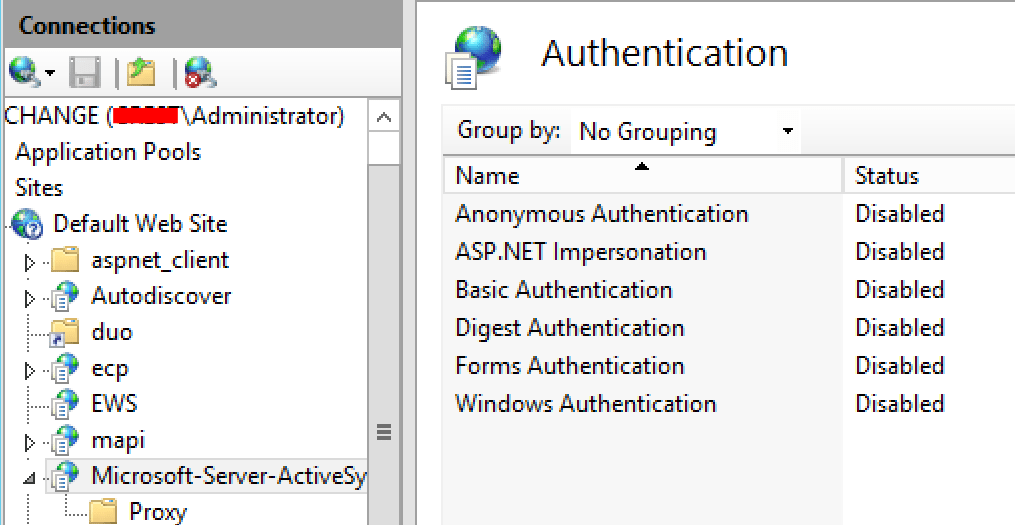
Disable ActiveSync Authentication
Enable 2-Factor Authentication
The majority of the attacks related to Microsoft Exchange require the threat actor to have already obtain the domain credentials of a user (Password Spraying, Phishing etc.). Enabling 2-factor authentication for all the exposed services like Outlook Web Access, Exchange Web Services and ActiveSync will prevent threat actors from:
- Getting access to the mailbox of the user and harvest sensitive data
- Conduct internal phishing attacks with higher success rate
- Achieve persistence on the network through arbitrary Outlook rules
- Compromise the domain
Even though that 2-factor authentication will provide an additional layer of security it should be treated only as a first line of defence. Several other remediations are required to prevent the implementation of the attacks.
Apply Critical Patches & Workarounds
Removing the following registry key is recommended by Microsoft to prevent NTLM authentication requests on the network loopback address of the Exchange server. This action will block the implementation of the attack that enables threat actors to add a forward rule to a target mailbox or add the compromised account as a delegate. The impact is retrieval of emails and impersonation of a user that will allow internal phishing attacks.
reg delete HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\Lsa /v DisableLoopbackCheck /f
Disable Loopback Check
Domain escalation is possible by abusing the Exchange Push Subscription. Microsoft has released patches to remediate the issue for various versions of Exchange servers by decreasing the permissions on Active Directory.
- KB4471391 – Exchange 2019
- KB4471392 – Exchange 2016
- KB4345836 – Exchange 2013
- KB4487052 – Exchange 2010
This technique requires valid Exchange credentials and is relying on EWS in order to perform the authentication. Disabling the authentication for Exchange Web Services (EWS) will prevent the attack.

Disable EWS Authentication
Similarly disabling Exchange Web Service mailbox access across the organisation will have the same result.
Get-Mailbox | Set-CASMailbox -EwsEnabled $false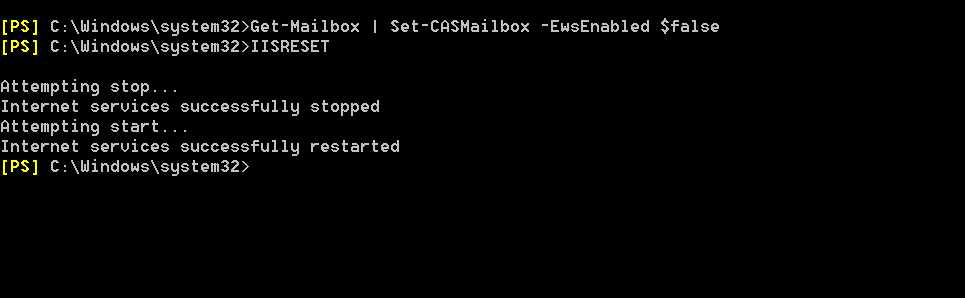
Disable EWS Access
Threat actors will not be able to authenticate with the Exchange in order to send the API call and they will receive the following errors in their terminals.

Prevent PrivExchange Attack
Benjamin Delpy presented on Twitter an alternative approach to mitigate the vulnerability by setting the MaxSubscriptions to zero. This setting will prevent the Exchange from sending any EWS notifications.
The following commands are required to be executed from the Exchange Management Shell:
New-ThrottlingPolicy -Name NoEWSSubscription -ThrottlingPolicyScope Organization -EWSMaxSubscriptions 0
Restart-WebAppPool -Name MSExchangeServicesAppPool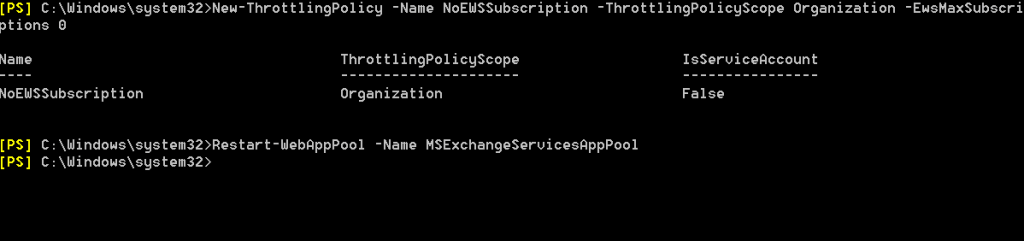
Create New Throttling Policy
Threat actors that will attempt to perform domain escalation by utilising the Exchange API call (Push Subscription) will not be allowed.
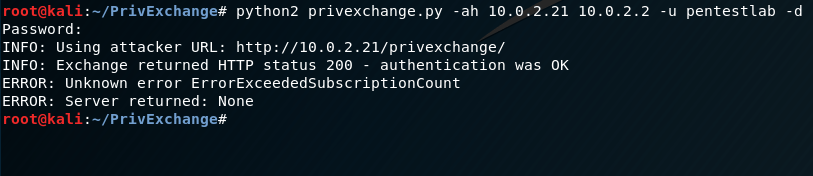
Subscriptions Disabled
Fully disabling EWS authentication will also NTLM relay attacks that will have as a target to obtain access to the mailbox of a user without cracking the password hash.
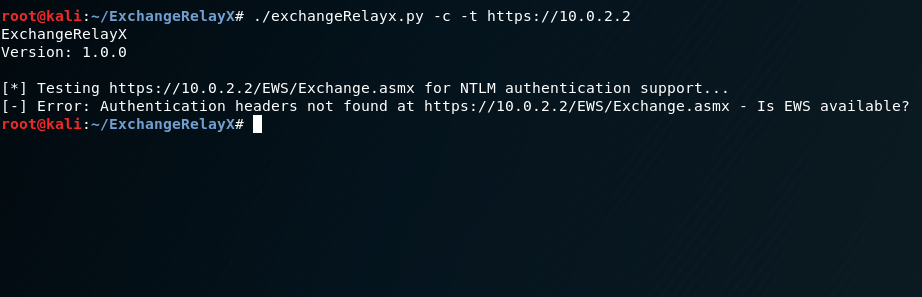
Prevent NTLM Relay Attack
Alternatively if authentication is required Microsoft Exchange can be configured to deny incoming NTLM traffic for all domain accounts.
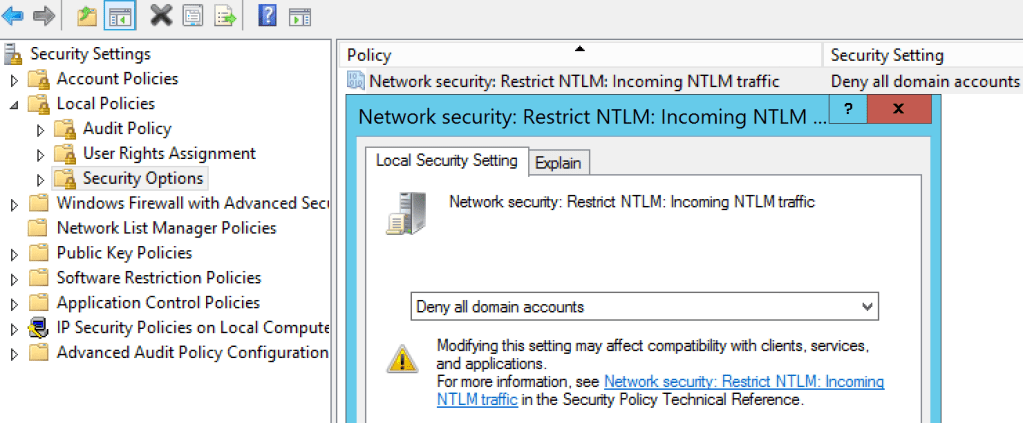
Restrict Incoming NTLM traffic
This will cause threat actors attempts that utilise NTLM relay as a technique to gain access to mailboxes and perform malicious actions to fail.
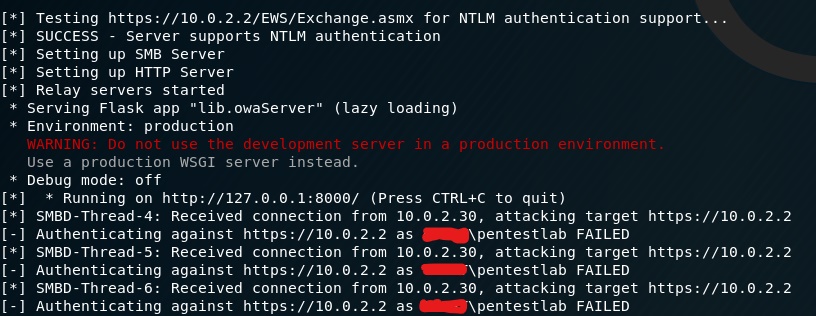
ExchangeRelayX Failed Authentication 
Python Script – CVE-2018-8581
Outlook Rules
Nick Landers discovered in 2015 that it is possible to abuse functionality of Microsoft Outlook (Rules and Alerts) in order to execute arbitrary code from a remote location (WebDAV or SMB Share) and gain persistence access on the host of the user. Microsoft has released a patch (KB3191893) which addresses the issue by creating a registry key. Zero value indicates that Outlook rules are disabled.
Outlook 2016
HKEY_USERS\<SID>\Software\Microsoft\Office\16.0\Outlook\Security\EnableUnsafeClientMailRules
Outlook 2013
HKEY_USERS\<SID>\Software\Microsoft\Office\15.0\Outlook\Security\EnableUnsafeClientMailRules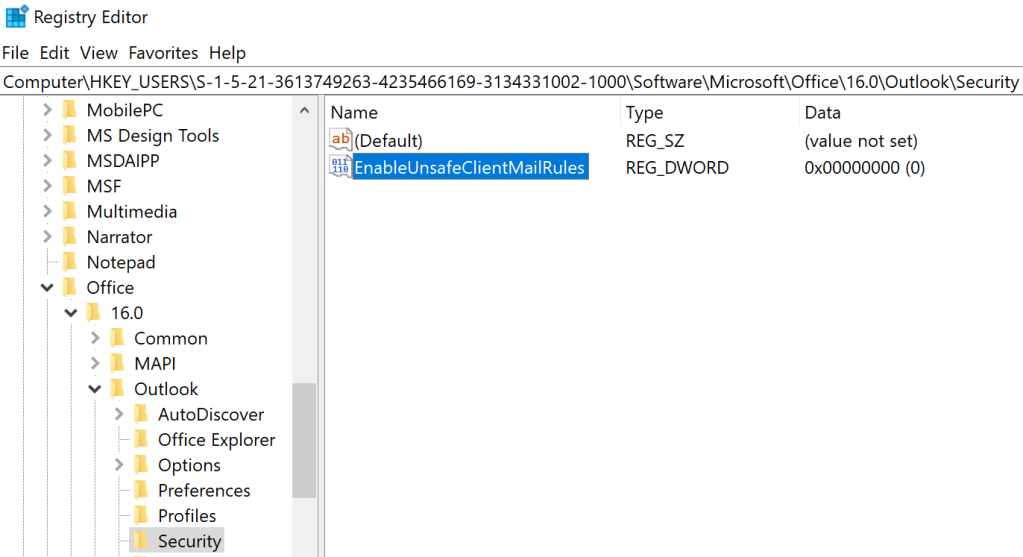
Disable Outlook Rules – Registry
Applying the Microsoft patch will disable permanently arbitrary client mail rules.
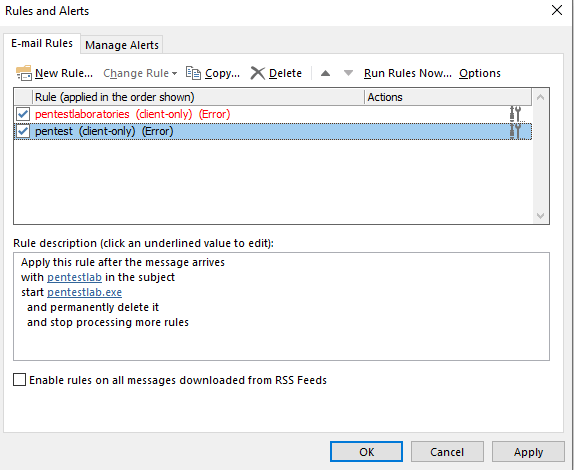
Outlook Rules Disabled
Outlook Home Page
Outlook Home Page feature can be utilised to inject a page that will execute an arbitrary payload on the system of the user. The payload will be triggered during browsing mailbox folder or when Microsoft Outlook is restarted. The discovery of this technique belongs to Etienne Stalmans and the implementation of this attack requires user credentials.
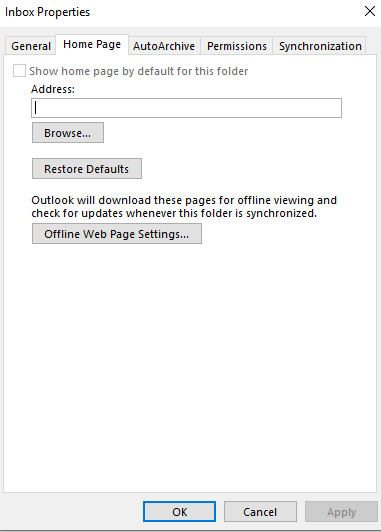
Outlook Home Page
Microsoft has released a patch (KB4011162) to address the vulnerability by removing the Home Page functionality from the Inbox Properties.
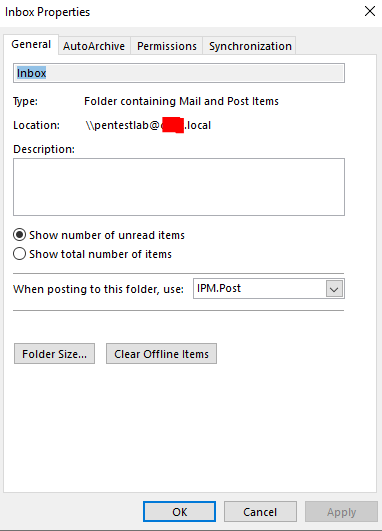
Outlook Home Page Removed
Enforce LDAP Signing & LDAP Channel Binding
Various attacks related to Microsoft Exchange abuse the trust relationship that exists with Active Directory in order to modify permissions and gain elevated access. Prevention of these attacks requires LDAP Signing and LDAP Binding to be enabled. Currently this setting is disabled by default however Microsoft intention is to release a security update (January 2020) that will enable LDAP Signing and LDAP Binding. Administrators can perform the change manually by modifying the Group Policy Management Editor.
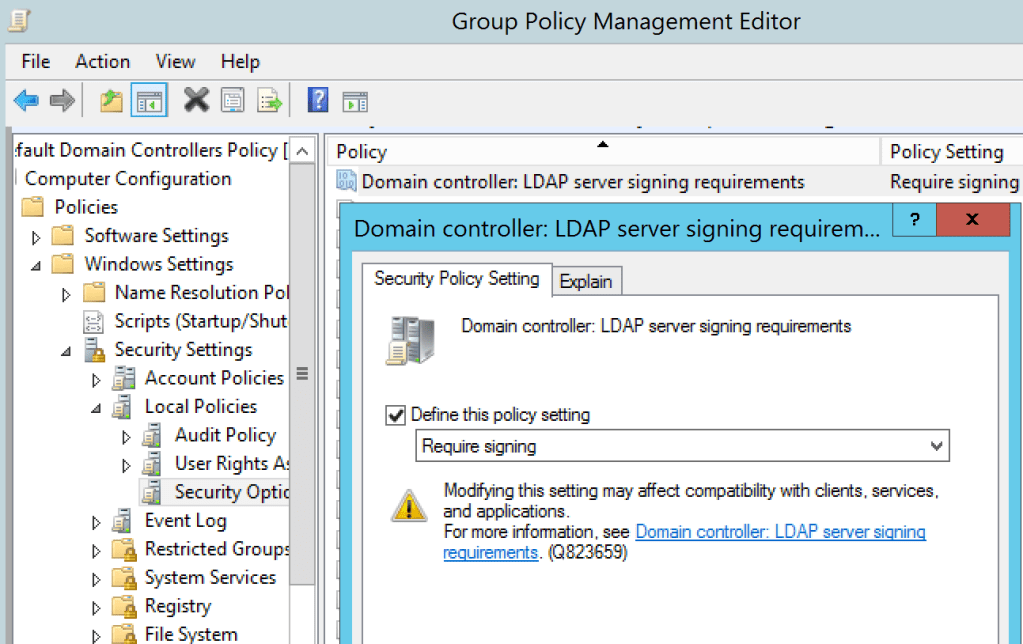
LDAP Server Signing
LDAP Signing can be enabled for clients through the Group Policy or Local Security Policy.
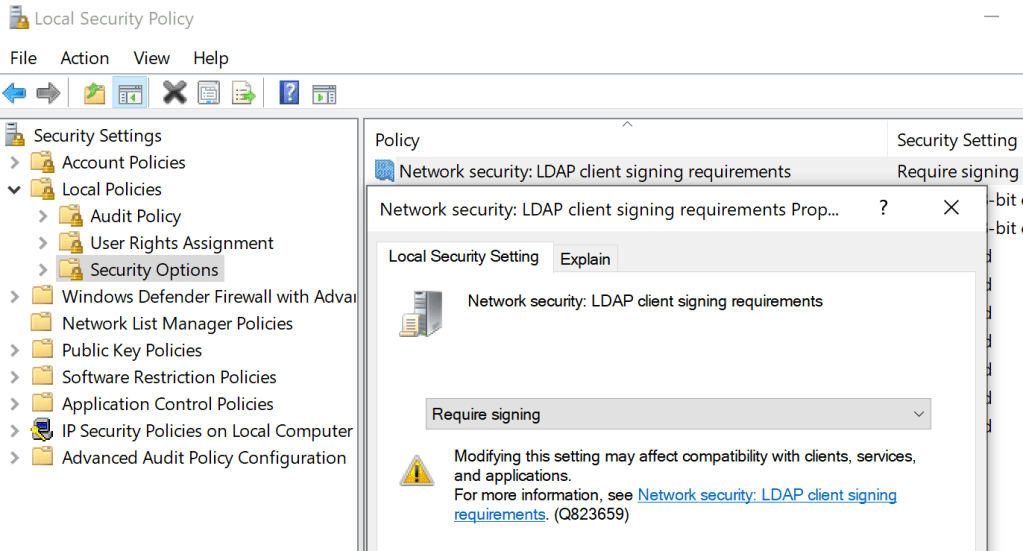
LDAP Client Signing
LDAP Binding can be enabled by creating a registry key in the following registry locations:
HKEY_LOCAL_MACHINE\System\CurrentControlSet\Services\NTDS\Parameters
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\<LDS instance name>\ParametersThe value 2 indicates that channel binding is enabled always.
LdapEnforceChannelBinding=2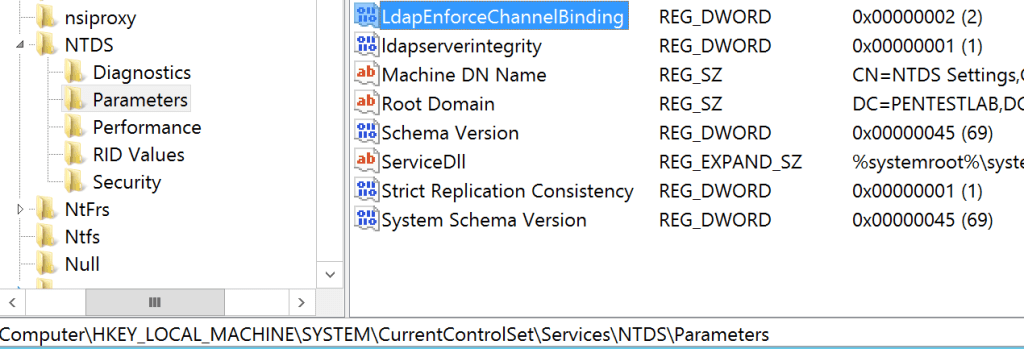
LDAP Channel Binding
Summary
Applying Microsoft security patches on time and implementing workarounds will improve organisations resiliency to cyber attacks that have as a target Microsoft Exchange. The following diagram summarises the patches and the mitigation fixes described in this article.
The table below correlates functionality that is being abused by threat actors, what they can achieve with the relevant Microsoft patch and CVE number.
| Functionality | Technique | Microsoft Patch | CVE Number |
| Outlook Rules | Code Execution | KB3191883 KB3191893 KB3191938 | N/A |
| Outlook Home Page | Code Execution | KB4011162 – 2016 KB4011178 – 2013 KB4011196 – 2010 | CVE-2017-11774 |
| Outlook Forms | Code Execution | KB3191883 | N/A |
| Push Subscription | Privilege Escalation | N/A | CVE-2018-8581 |
| Push Subscription | Domain Escalation | KB4471391 – 2019 KB4471392 – 2016 KB4345836 – 2013 KB4487052 – 2010 | CVE-2019-0686 CVE-2019-0724 |
If you are interested to learn more about how Pentest Laboratories and our custom cyber attack scenarios can improve your organisation readiness against cyber threats please contact us.